- Protecting your computer from viruses is essential if you want to keep your data safe and your system running smoothly.
- There are a few simple steps you can take to reduce the risk of infection and ensure that your computer is protected.
What is a Computer Virus
A computer virus is a code or program that can copy itself and infect a computer without the user’s knowledge or permission. A virus might corrupt or delete data on your computer, use your email program to spread itself to other computers, or even erase everything on your hard drive.
And if you want to know about Lenovo laptops or shop accessories, or other buying guides, I’ve got you covered in my other articles as well.
THIS POST MAY CONTAIN AFFILIATE LINKS. As an Amazon Associate, I earn from qualifying purchases. PLEASE READ MY DISCLOSURE FOR MORE INFO.
Tips to Protect Your Computer From Viruses and Malware
Take steps to protect your computer from viruses and malware.
1. Use an Antivirus and Anti-Malware Program
Protecting your computer from viruses starts with a strong antivirus program that is kept up-to-date. You should also install an anti-malware program and scan your computer regularly. Be careful what you click on when you are online.
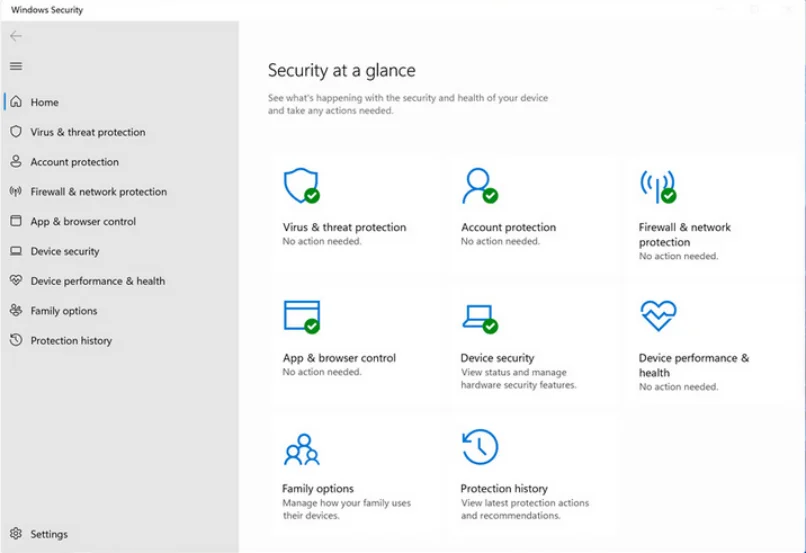
Windows has built-in virus protection called Microsoft Defender Antivirus. If you are using another antivirus program, make sure it is always up to date.
Open Microsoft Defender Antivirus in Windows 11:
- Click the Start menu. In the search bar, type “virus” and click Virus & threat protection.
- Under Current threats, you’ll see how many threats were found and removed in the last scan. If no threats were found, you’ll see a message that says “No active threats were found.”
- Under Virus & threat protection settings, click manage settings.
- Ensure Real-time protection and everything else is turned on.
Set up Automatic Scans
Windows Defender is set to run weekly by default, but you can schedule it to scan more often. To do this, open Windows Defender and find the “Scan Options” link, and select the time you would like for scans to run.
2. Keep Your Software up to Date
Make sure that your operating system and internet browser are up-to-date. Updates often include security features that can help protect your computer from new threats. It is easy to check for updates, just set them to install automatically.
Check for software updates in Windows 11:
- Click the Start menu. In the search bar, type “update” and click Check for updates.
- You can install or check for updates, as well as look at the update history.
3. Avoid Email Attachments from Unknown Senders
Email attachments can be a way for viruses to enter your computer. Be cautious about opening email attachments, even if they are from someone you know. Also, be careful what you download from the internet and only download files from trusted sources.
An email attachment will look like a regular file attached to an email. They can be in different formats like a PDF, image, or Microsoft Office document.
4. Backup Your Computer
Back up important documents and files to an external hard drive or cloud storage service. An example of cloud storage is Google Drive. That way, if your computer does get infected, you can restore your files.
To use Google Drive:
- Go to drive.google.com.
- Sign in with your Google Account.
- Click New.
- Upload files and folders from your computer.
5. Use your Firewall
A firewall can help protect your computer from viruses and other malware by blocking malicious traffic before it reaches your computer. Windows has built-in firewall protection, or you can use another program like Norton Internet Security. It should be enabled by default but you can check by opening the Windows Firewall and making sure the “On” switch is selected.
6. Use Strong Protection
Strong protection includes good passwords and encryption. A password should be at least eight characters long and include a mix of uppercase and lowercase letters, numbers, and symbols. You should never use the same password at more than one site.
7. Use a Password Manager:
You can use a password manager to help keep track of your passwords and generate strong passwords. A password manager is a program that stores your passwords in an encrypted format.
ALSO READ: How To Use Public WiFi Safely | Advice
Definitions
Malware
Malware is short for malicious software and is any software that is designed to harm your computer, steal personal information, or otherwise cause damage.
Some types of malware are viruses, spyware, Adware, Trojans, and rootkits.
Virus
A virus is a type of malware that can copy itself and spread to other computers. A virus might corrupt or delete data on your computer, use your email program to spread itself to other computers, or even erase everything on your hard drive.
Spyware
Spyware is a type of malware that can track your online activity and collect personal information, such as passwords, without your knowledge.
Adware
Adware is a type of malware that displays advertising on your computer, often in the form of pop-up ads.
Trojan
A Trojan is a type of malware that masquerades as legitimate software but is actually designed to damage your computer or steal your personal information.
Rootkit
A rootkit is a type of malware that gives an attacker access to your computer and allows them to make changes without your permission.
What Are the Symptoms of A Computer Virus
So how do you know when you have a computer virus? Here are some common symptoms:
- Your computer is running slowly.
- Your internet browser’s homepage has changed without your permission.
- Pop-up ads appear when you’re not expecting them.
- You can’t access certain websites, or your internet connection is slower than usual.
- Files or programs won’t open.
- You see strange error messages.
- Your computer crashes or restarts on its own.
- You notice new, unknown files on your hard drive.
These are some of the more common issues you may see, but not all viruses display these symptoms. In some cases, a virus might do nothing more than replicate itself on your computer. In other cases, it might delete files or damage your hard drive.
How To Remove A Computer Virus
We now get to the difficult part, which is removing computer viruses. If you suspect that your computer has a virus, the best thing to do is run an antivirus program like Microsoft Defender or Norton Internet Security. You can also download a free tool by Malwarebytes to run an additional scan.
These programs will scan your computer for viruses and remove any that they find. Or else, they might be able to quarantine the virus to prevent it from spreading or infecting other files.
If you can’t access your antivirus program or if the virus is blocking it, you may need to boot your computer into Safe Mode. This will prevent the virus from running and allow you to remove it.
Tip: It is a good idea to create a USB virus scan tool beforehand so you have it ready if you ever need to use it. Create your own USB virus or malware scanner by following these steps:
- Download an antivirus program like Kaspersky Rescue Disk or Sophos Bootable Anti-Virus onto a clean computer.
- Connect a USB drive to the computer. You need at least a 1GB USB drive.
- Open the antivirus program and choose the option to create a bootable USB drive.
- Follow the instructions to create the bootable USB drive.
- Once the process is complete, disconnect the USB drive and connect it to your infected computer.
- Boot your infected computer from the USB drive.
- Once the program starts, follow the instructions to scan your computer for viruses and remove any that are found.
Alternatively, if you can still access Windows, run the Microsoft Defender Offline tool from Virus & threat protection page. This will reboot your computer and run its own scan.
J.S. is the owner, content creator, and editor at Upgrades-and-Options.com. I’ve worked in the IT and Computer Support field for over 20 years. The server hardware in my computer labs has mostly been IBM, but I’ve supported Dell, HP, and various other hardware. In addition, as part of my lab administrator responsibilities, I’ve learned, supported, and repaired/upgraded network hardware such as Cisco routers and switches. READ FULL BIO >>
- Best Laptops for AI and Machine LearningDiscover the top 5 laptops for AI and Machine Learning. We review high-performance machines perfect for deep learning, data science, and neural networks. Artificial Intelligence (AI) and Machine Learning (ML) are no longer futuristic concepts—they are the tools shaping our daily lives right now. From developing complex neural networks to training large language models (LLMs) locally, the hardware demands for these tasks have… Read more: Best Laptops for AI and Machine Learning
- Upgrading SSD Storage in the ThinkPad X9-15 Gen 1 Aura EditionUpgrading SSD Storage and Analyzing Memory in the ThinkPad X9-15 Gen 1 Aura Edition Upgrade Your ThinkPad X9-15 SSD Like a Pro: A Technical Guide The ThinkPad X9-15 Gen 1 Aura Edition (Machine Types 21Q6 and 21Q7) is designed as a premium device. While memory is permanently fixed, users can easily expand storage capacity, as the M.2 Solid-State Drive (SSD) is designated as… Read more: Upgrading SSD Storage in the ThinkPad X9-15 Gen 1 Aura Edition
- How Quantum Computing Could Impact Everyday LaptopsQuantum computing may sound like science fiction, but its potential to revolutionize technology is very real. Unlike classical computing, which processes information using bits as 0s and 1s, quantum computing leverages the strange and exciting principles of quantum mechanics — like superposition and entanglement — to perform calculations at speeds previously thought impossible. This unprecedented power isn’t just about tackling complex simulations or… Read more: How Quantum Computing Could Impact Everyday Laptops
- What Is The Difference Between Lenovo’s Pens? (with Part Numbers)Do you ever find yourself writing with an old-school pen or even worse a pencil? As you pry your fingers off that last-century writing device, ask yourself if there isn’t a better way. Well ask no more, there is a whole world of digital pens out there just waiting for you to discover.I went through this same process and wanted to find out… Read more: What Is The Difference Between Lenovo’s Pens? (with Part Numbers)
- Legion 5 Laptop Upgrade Guide: Game Like a ProThis article serves as your ultimate guide to upgrading your Lenovo Legion 5 laptop with RAM and SSD, unlocking its potential to deliver unbeatable gaming performance. With over two decades of expertise in the tech industry and countless successful upgrade projects under my belt, I’ve distilled all my knowledge into this comprehensive guide. You’ll learn, step by step, how to upgrade the RAM… Read more: Legion 5 Laptop Upgrade Guide: Game Like a Pro